Products
Buy options
€16.50| Model Number | c202 |
|---|---|
| Form-factor | dongle |
| Functions | TOTP sha1 |
| Dimensions | 49×26×8 mm |
| Weight | 16.8 gr |
| Programmable | |
| Product ID | T2-1 |
| Wordpress | fully compatible | |
|---|---|---|
| Azure On-Prem MFA Server | fully compatible | |
| Azure Cloud MFA / Office 365 AD Premium P1 or P2 | fully compatible | |
| Watchguard AuthPoint | fully compatible | |
| ESET Secure Authentication | fully compatible | |
| Google Account | not compatible | |
| Meraki Dashboard | not compatible | |
This list is far from complete; we only highlight some featured supported systems. Listing all compatible systems would make the list very long. Check with us for more details: |
contact us |
|
If the system you are using is not included in the compatibility list, it does not necessarily indicate incompatibility. We encourage you to refer to our integration guides page or get in touch with us for more information. | ||
Please check product and platform compatibility before placing an order
All pictures shown are for illustration purpose only. Actual product may slightly vary due to product enhancement or other reasons.
Note: The backplate plastic color may differ depending on the production batch – images are not contractual. Some units may have a white backplate, others black.
Specifications:
- Built-in Button, 6 Character LCD Screen
- Security Algorithm: TOTP as per RFC6238 with SHA1 hash
- OTP Length: 6 digits
- OTP Time interval: 30 seconds
- Dimensions: 49.8 x 26 x 8.25mm
- Water resistance: IP67
- Secret hash: random - factory programmed
- Hardware Certification: RoHS Compliant
- Operating Temperature: -10°C .. 50°C
- Tamper Evident / Tamper Protection
- Battery Type: Standard Lithium Battery
- Battery Lifetime: 5-7 Years (depending on usage)
Obtaining the seeds/secrets/CSV files for TOTP tokens
The process of requesting factory-set seeds for Token2 hardware tokens is described here.
Independent Compliance Check
- RFC6238 compliance confirmed by CertX, the first swiss accredited certification body for product certification in the scope of industrial cybersecurity and functional safety.
Time drift and other parameters
This is a classic TOTP token with factory-set seeds. Parameters such as the hash algorithm (SHA-1 or SHA-256), seeds, or internal clock cannot be changed. It can only be used with systems that allow seed import and implement RFC-compliant time drift compensation.Related products
Blog
04-04-2026
Understanding FIDO User Verification Modes and the always_uv Setting
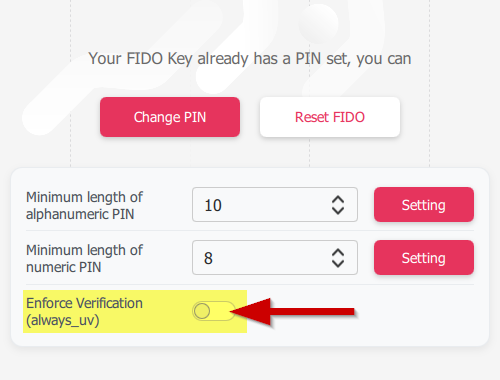 Token2 R3.3 and later FIDO2 keys enforce user verification by default with always_uv = true, improving security, though some platforms and apps like Windows 10, macOS, and certain legacy clients may fail to handle this override correctly.
Token2 R3.3 and later FIDO2 keys enforce user verification by default with always_uv = true, improving security, though some platforms and apps like Windows 10, macOS, and certain legacy clients may fail to handle this override correctly.
05-03-2026
Introducing TOTPVault — self-hosted TOTP management for teams
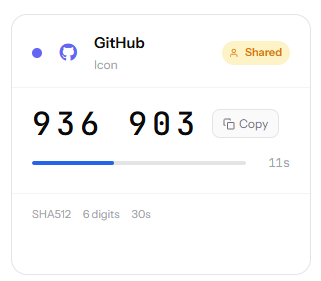 Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
21-12-2025
Android, NFC, and the Missing Piece of WebAuthn
 For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.
For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.










