 Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
TOTPVault takes a different approach: secrets never leave the server. OTP codes are generated in PHP on the backend, your secrets are AES-256-GCM encrypted at rest, and teammates get access to the codes — not the keys. Revoke access in one click, no secret rotation required.
What it does
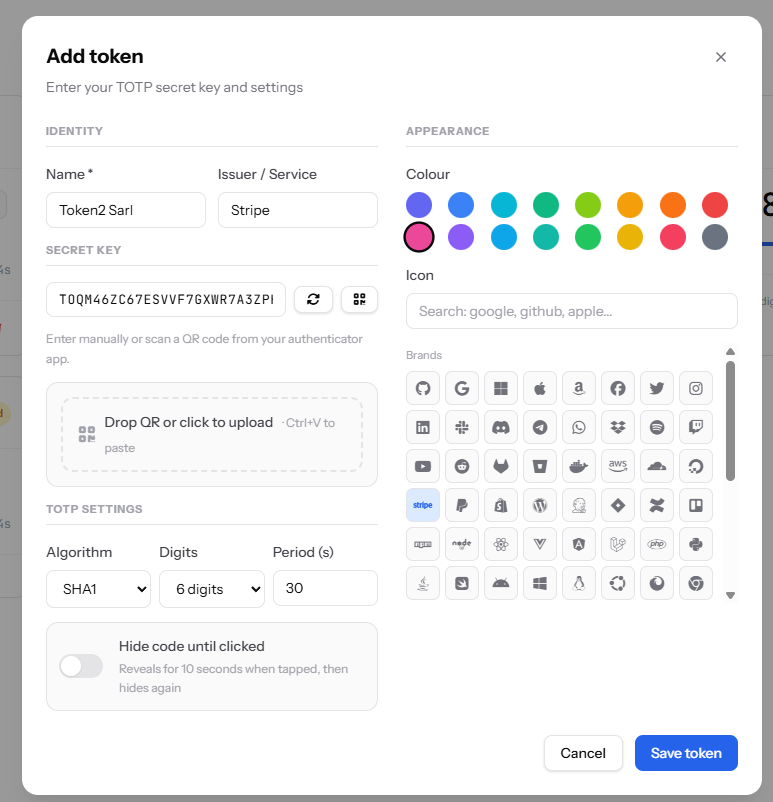
- Server-side RFC 6238 — SHA1, SHA256, SHA512 · 6, 8, or 10-digit codes · configurable periods
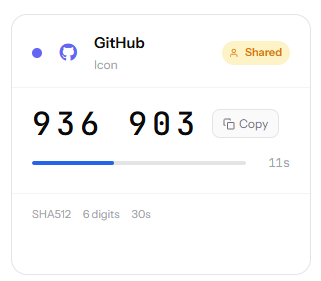
- Token sharing — invite colleagues by email; they see live codes, never the secret
- Multiple login methods — OAuth via Google, Microsoft, or GitHub; passwordless magic links for everyone else
- QR code import — drop a screenshot of any
otpauth://QR code to import a token instantly, decoded entirely client-side - Hide mode — mask a code until tapped; auto-hides after 10 seconds
- No dependencies — plain PHP 8.1, MySQL, and a MailerSend account for email; no Composer, no build step
The philosophy
A tool that handles authentication secrets should be as small and auditable as possible. TOTPVault is five source classes, one router, and two templates. You can read the whole codebase in an afternoon.
TOTPVault GitHub Repo
Live Demo
tools
Subscribe to our mailing list
Want to keep up-to-date with the latest Token2 news, projects and events? Join our mailing list!
