Using Token2 hardware tokens with Django
 Django is a high-level Python web framework that encourages rapid development and clean, pragmatic design. Built by experienced developers,
it takes care of much of the hassle of web development, so you can focus on writing your app without needing to reinvent the wheel.
It’s free and open source.
Django is a high-level Python web framework that encourages rapid development and clean, pragmatic design. Built by experienced developers,
it takes care of much of the hassle of web development, so you can focus on writing your app without needing to reinvent the wheel.
It’s free and open source.Django allows using Token2 programmable tokens or Token2 classic tokens for two-step verification.
Requirements:
• Access to the Django project environment.
• Admin access to the Django Administration.
• A Token2 programmable or classic token.
• An iPhone or Android device with NFC*.
[* Android and Windows versions are available for all models, but this guide will use the iPhone app as an example. iPhone apps are compatible with "-i" models only].
Step 1. Enable an MFA method
1) Go to the Python console and add the django-otp and qrcode packages.pip install django-otp qrcode
2) Open the settings.py file and append the following values to the INSTALLED_APPS array:
'django_otp'
'django_otp.plugins.otp_totp'
3) Append the value to the MIDDLEWARE array:
'django_otp.middleware.OTPMiddleware'
4) Open the urls.py file and add:
from django_otp.admin import OTPAdminSite
class OTPAdmin(OTPAdminSite):
pass
from django.contrib.auth.models import User
from django_otp.plugins.otp_totp.models import TOTPDevice
admin_site=OTPAdmin(name='OTPAdmin')
admin_site.register(User)
admin_site.register(TOTPDevice)
And an additional path to the urlpatterns array in this file:
path('totpadmin/', admin_site.urls)
5) Run ./manage.py migrate from the console to save changes to your models.
6) As a result, we will get two login URLs : http://127.0.0.1:8000/admin/ and http://127.0.0.1:8000/totpadmin/
The first link is the default administration login URL, which does not ask for in 2FA -TOTP. And the second is a just created link with forced TOTP.
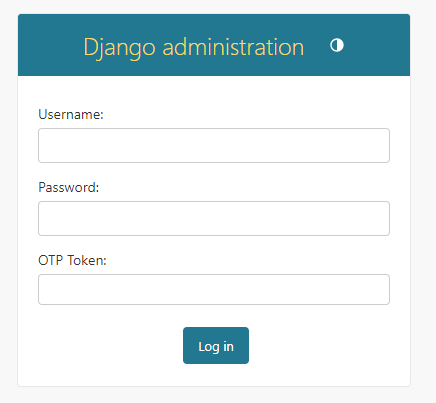
We cannot login using the second link yet because no users have 2FA enrolled.
7) Let's create a new TOTP device and assign it to the existing user. Log in with the default link and create a TOTP device.
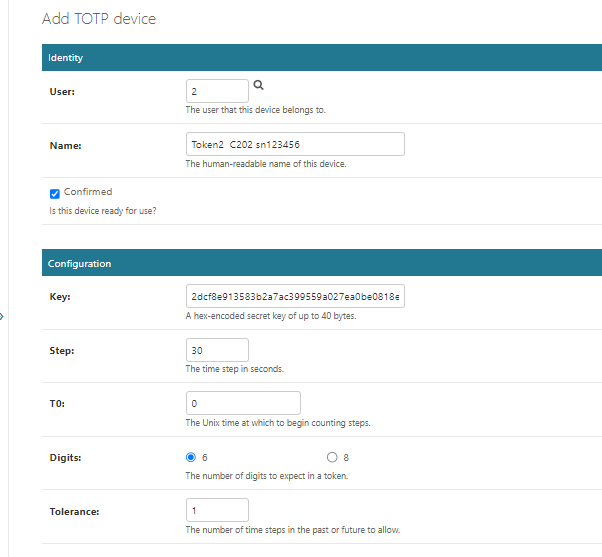
Note: For hardware tokens that are over 2 years old, it is recommended to use a higher tolerance value.
-User: Browse for the user to be mapped.
-Name: Give some name for the new TOTP device.
-Key: By default, the system gives a random secret key,but you can also use your own secret key. In the case of classic tokens, there is no need for the next step.
Keep other settings by default, and click the Save button to save changes.
8) Then click QRcode to open OTP enrollment page, which contains a QR code that you will scan using one of the provisioning tools in the next step.

Step 2. Provision the token
- Launch the NFC burner app on your Android device and hit the "QR" button
- Point the camera to the QR code shown on the account page. Upon a successful QR scan, the camera window should disappear
- Turn on the token and touch it with your phone (make sure it is overlapped by the NFC antenna) and click "Connect" on the app
- Upon successful connection, click the "Burn seed" button (the button will become active only if NFC link is established).
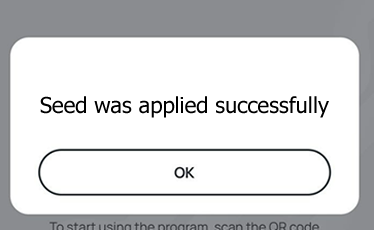
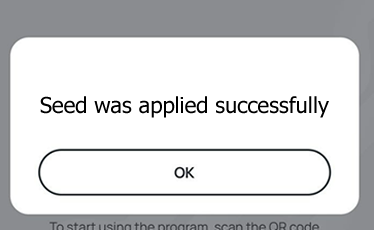
- A message box similar to the one below will be shown upon successful completion
Follow the steps below to perform setting the seed for your token using Windows App.
1. Launch the exe file, then select the NFC device from the drop-down list and click on "Connect". You should see a message box notifying about a successful operation.
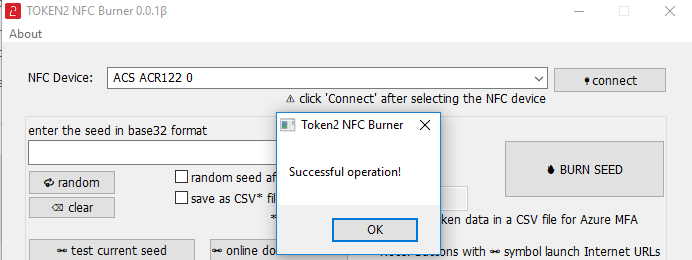
2. Enter or paste the seed in base32 format, or use one of the QR scanning methods to populate this field
3. Place the token onto the NFC module and wait for its serial number to appear.
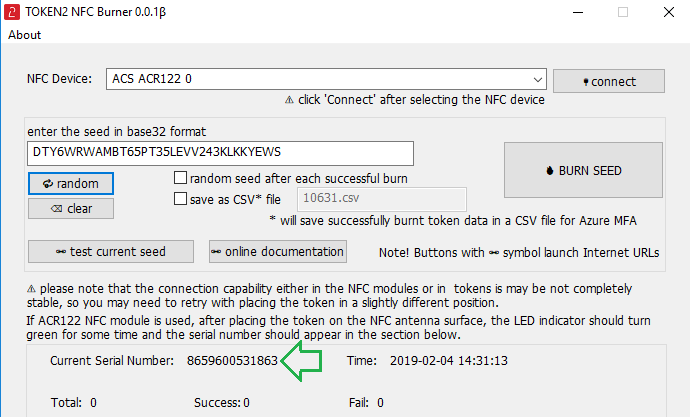
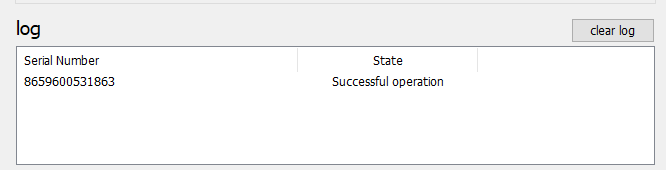
4. Click on "Burn seed" button. A log entry with the serial number and "Successful operation" text will be logged in the log window.
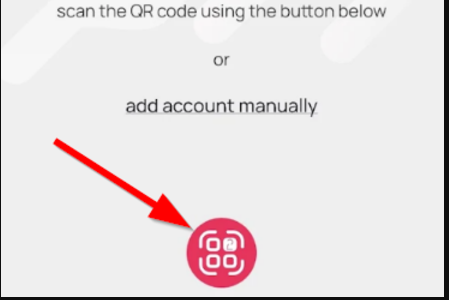
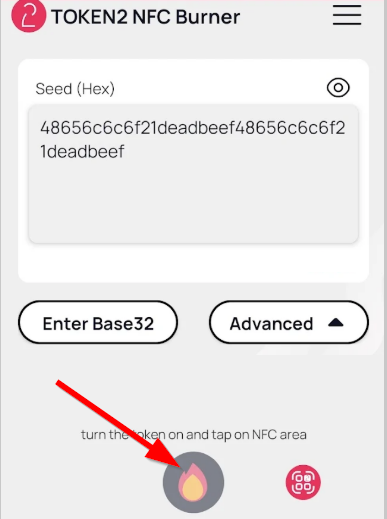
- Launch the NFC burner app on your iPhone device and hit the "scan QR" button
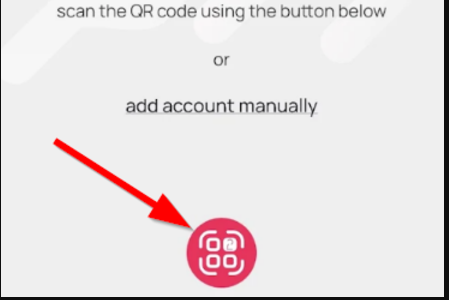
- Point the camera to the QR code shown on the account page. Upon a successful QR scan, the camera window should disappear and the seed field will be populated with the hex value of the seed. Touch the Burn button to continue.
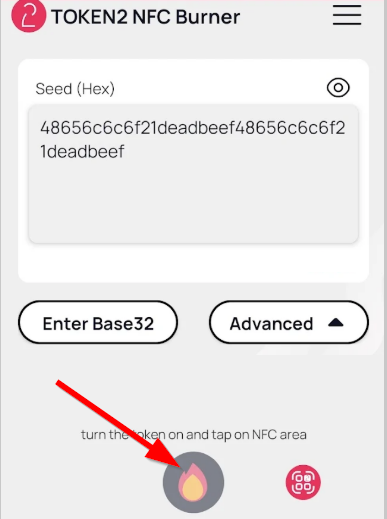
- When an NFC prompt similar to the one below is shown, turn on the token and touch the top of your iPhone with the token.
- A message box similar to the one below will be shown upon successful completion
Please note that the procedures above are shown only as examples and are valid to single profile TOTP tokens only. The procedure for multi-profile and USB-programmable devices are similar but slightly different
Step 3. Connect using 2FA
When the token provisioning is done, turn the token off and back on. Enter the login, password, and OTP from the token. After successful authentication, you will be able to login to the Django administration.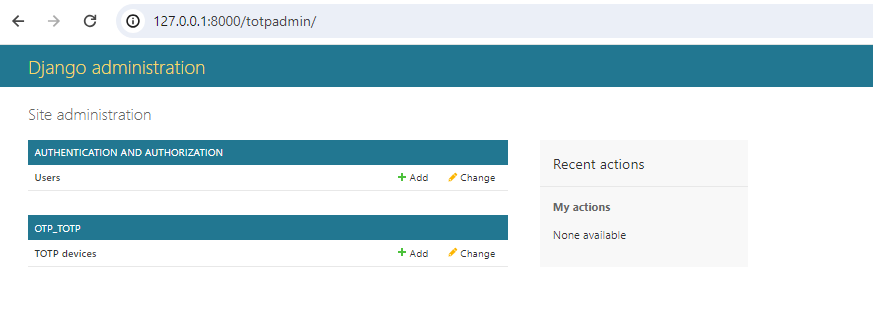
Subscribe to our mailing list
Want to keep up-to-date with the latest Token2 news, projects and events? Join our mailing list!
