23-10-2018
Microsoft Azure Cloud MFA OATH hardware tokens support (public preview)
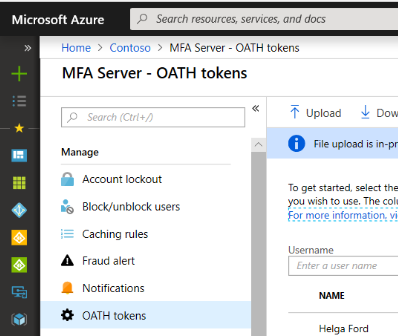 Microsoft has recently (around 15/10/2018) announced the availability (public preview) of [classic] OATH hardware tokens with its cloud-hosted Azure MFA Server.
Microsoft has recently (around 15/10/2018) announced the availability (public preview) of [classic] OATH hardware tokens with its cloud-hosted Azure MFA Server.
integration guides
27-09-2018
Which Token2 hardware token is right for my Azure MFA?
 Microsoft Azure Multi-Factor Authentication (MFA) helps safeguard access to data and applications while maintaining simplicity for users. It provides additional security by requiring a second form of authentication and delivers strong authentication via a range of easy to use authentication methods, hardware tokens being one of them.
Microsoft Azure Multi-Factor Authentication (MFA) helps safeguard access to data and applications while maintaining simplicity for users. It provides additional security by requiring a second form of authentication and delivers strong authentication via a range of easy to use authentication methods, hardware tokens being one of them.
integration guides
25-09-2018
Enable hardware token based two factor authentication for Meraki Dashboard account
 Meraki Dashboard has the option of requiring two-factor authentication for logging into. In addition to the default option, which is SMS, one of the options available to users is the Google Authenticator (which can be replaced by our mini-OTP1 hardware token).
Meraki Dashboard has the option of requiring two-factor authentication for logging into. In addition to the default option, which is SMS, one of the options available to users is the Google Authenticator (which can be replaced by our mini-OTP1 hardware token).
integration guides
23-09-2018
Enable hardware token based two factor authentication for your Stripe account
 Two-step authentication protects your Stripe account with an additional level of security. When you log in from a new device, Stripe will ask for both your password and a unique code from your hardware token. Even if someone has your password, they will not be able to log into your account without also having access to your token.
Two-step authentication protects your Stripe account with an additional level of security. When you log in from a new device, Stripe will ask for both your password and a unique code from your hardware token. Even if someone has your password, they will not be able to log into your account without also having access to your token.
integration guides
21-09-2018
Token2 TOTP tokens - product line expansion
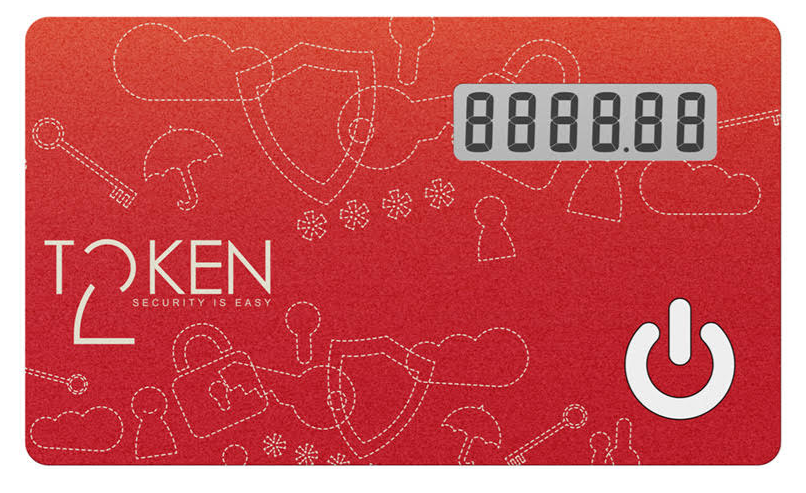
 Based on customers' feedback we found that there was more demand for different types of TOTP tokens. We are currently arranging expanding our product line with 3 more token types which are hereby announced. This will include 2 classic tokens, and an OTP Display card (nonprogrammable, credit card format).
Based on customers' feedback we found that there was more demand for different types of TOTP tokens. We are currently arranging expanding our product line with 3 more token types which are hereby announced. This will include 2 classic tokens, and an OTP Display card (nonprogrammable, credit card format).
product updates
19-09-2018
Token2 TOTPRadius 0.2.3 has been released
 Token2 TOTPRadius is a standards based RADIUS server designed for two-factor authentication.
Token2 TOTPRadius is a standards based RADIUS server designed for two-factor authentication.
product updates news
16-09-2018
Exotics : Paper Based MFA
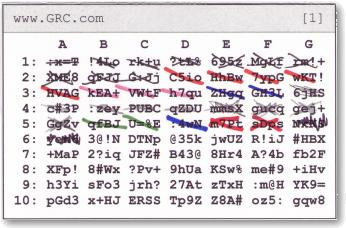 Multifactor authentication is not always something complex and expensive. There are a number of implementations of two factor authentication systems that use a list of one-time passwords printed on a piece of paper. In this post, we will review two examples of such systems.
Multifactor authentication is not always something complex and expensive. There are a number of implementations of two factor authentication systems that use a list of one-time passwords printed on a piece of paper. In this post, we will review two examples of such systems.
theory history
11-09-2018
Token2 miniOTP-1 programmable token facelift
 In about a month we will be slightly changing the visual appearance of our miniOTP-1 token while leaving its underlying engineering or design intact.
In about a month we will be slightly changing the visual appearance of our miniOTP-1 token while leaving its underlying engineering or design intact.
product updates
Subscribe to our mailing list
Want to keep up-to-date with the latest Token2 news, projects and events? Join our mailing list!