Hardware MFA tokens for Office 365 / Azure cloud Multi-factor authentication
FAQ - Office365/ Azure AD (Microsoft Entra ID) MFA
With over 30 million users globally Office 365 from Microsoft is one of the most popular productivity software subscription suites on the enterprise market. In this guide, we will give you the full step-by-step instructions on arranging protection with hardware tokens for Office 365 without a need to obtain Azure AD (Microsoft Entra ID) Premium license. Please note that without Premium license, the enrollment is done on behalf of the end-user.

How to use Token2 programmable tokens with Azure MFA
Token2 programmable tokens are a "drop-in" replacement of mobile applications such as Google Authenticator or Token2 Mobile OTP. If you are using Office 365 with Azure MFA protection enabled, you can use our programmable tokens as an alternative to mobile application method by following the instructions below. Please note that this requires no administrative privileges and any user can benefit from this method. The only prerequisite is an NFC-enabled device running one of our apps.
Step1. Install one of the burner apps and make sure your token is accessible via NFC.
For example, make sure the serial number is shown on the screen if you use the Windows NFC Burner app. For Android, you can test NFC access by "retrieve token data" button of the app: push the button on the device and hold it close to the NFC antenna of your device (on the phones it is usually below the camera on the back). Be aware of NFC stability issues with some devices described here.Step 2. Enable or reconfigure Authenticator app on your Office 365 account
On a desktop browser, navigate to MFA setup page and from the Security info page, select "Add Method", and "Authenticator App" from the list.
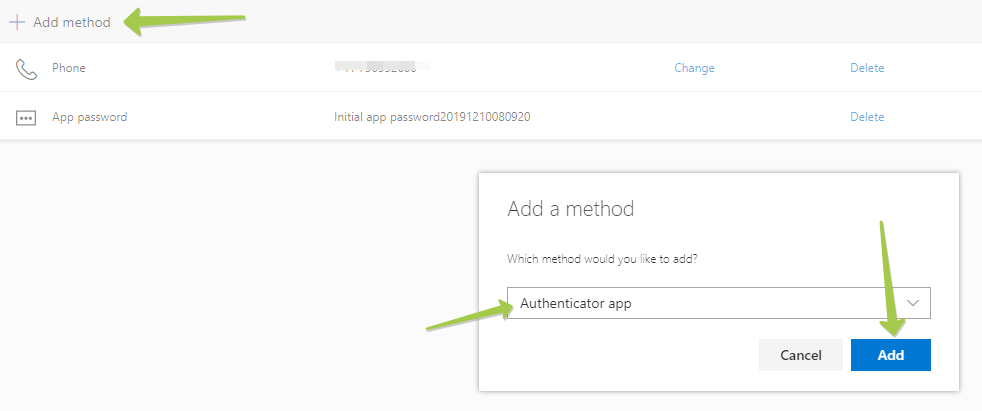
Click "Add" to proceed to the next step. By default, it prompts to use Microsoft Authenticator, which uses a different OTP protocol, which cannot be transferred over to our hardware tokens. Please click on "I want to use a different authenticator app" to generate a TOTP QR code instead.
Note: this step is very important, make sure this option is correctly selected!
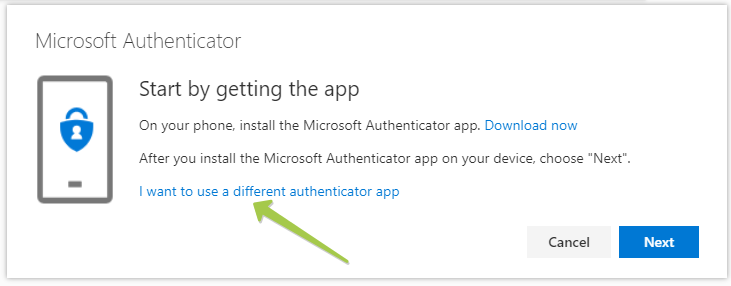
On the next window, click "Next" to get the QR code displayed on the screen
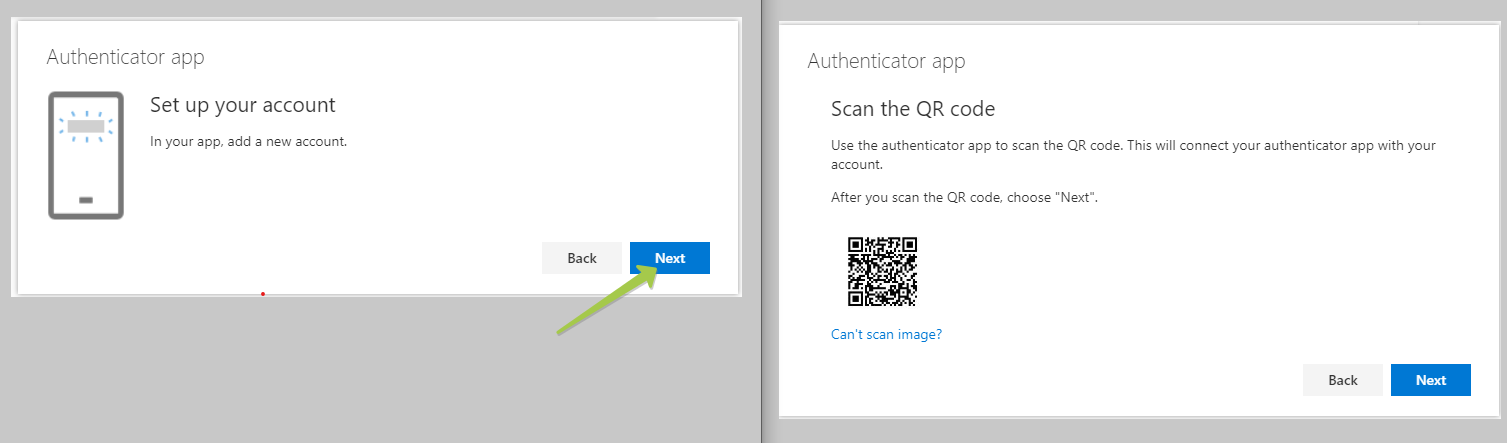
Keep this window open and proceed to Step 3 on your mobile device.
Step 3. Burn the token with Token2 Burner App
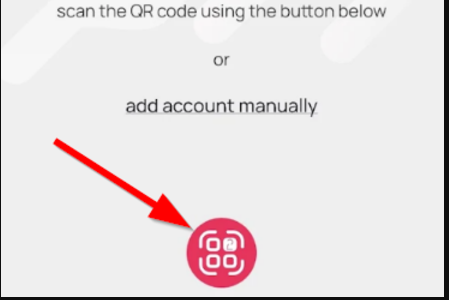
- Launch the NFC burner app on your Android device and hit the "QR" button
- Point the camera to the QR code shown on the account page. Upon a successful QR scan, the camera window should disappear
- Turn on the token and touch it with your phone (make sure it is overlapped by the NFC antenna) and click "Connect" on the app
- Upon successful connection, click the "Burn seed" button (the button will become active only if NFC link is established).
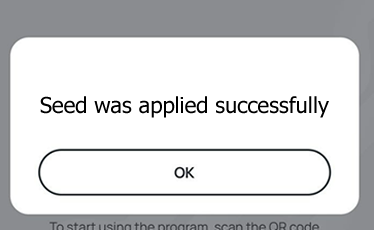
- A message box similar to the one below will be shown upon successful completion
Follow the steps below to perform setting the seed for your token using Windows App.
1. Launch the exe file, then select the NFC device from the drop-down list and click on "Connect". You should see a message box notifying about a successful operation.
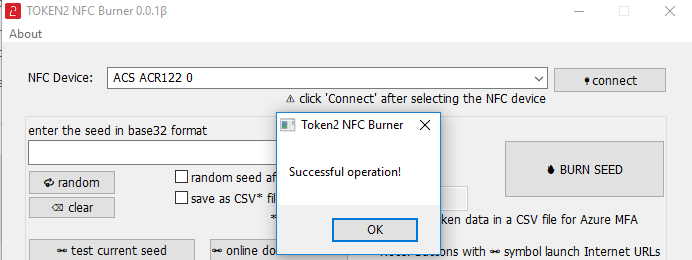
2. Enter or paste the seed in base32 format, or use one of the QR scanning methods to populate this field
3. Place the token onto the NFC module and wait for its serial number to appear.
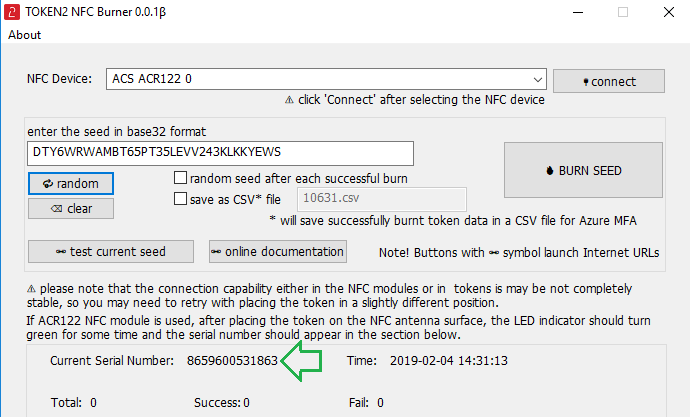
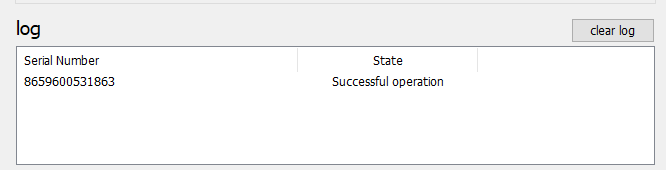
4. Click on "Burn seed" button. A log entry with the serial number and "Successful operation" text will be logged in the log window.
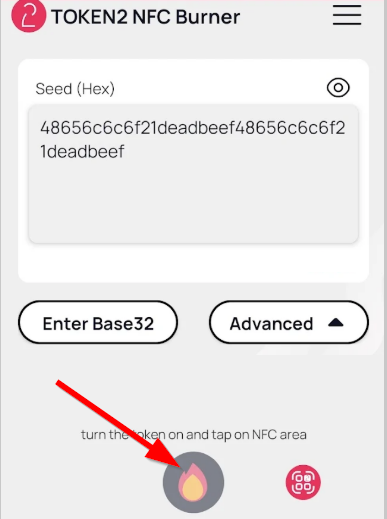
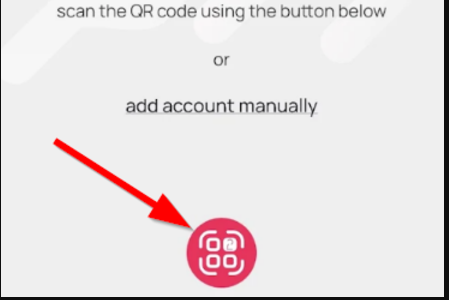
- Launch the NFC burner app on your iPhone device and hit the "scan QR" button
- Point the camera to the QR code shown on the account page. Upon a successful QR scan, the camera window should disappear and the seed field will be populated with the hex value of the seed. Touch the Burn button to continue.
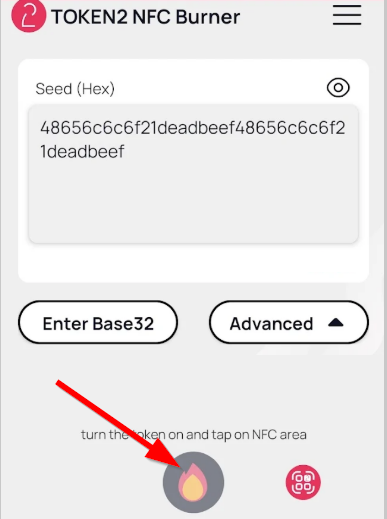
- When an NFC prompt similar to the one below is shown, turn on the token and touch the top of your iPhone with the token.
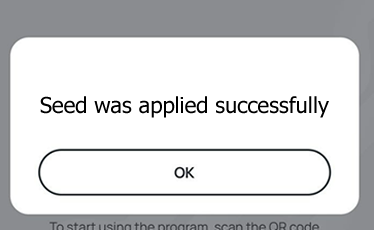
- A message box similar to the one below will be shown upon successful completion
Step 4. Verify the token and complete the enrollment
After the burn process is completed, click Next and proceed with OTP verification. To verify the OTP, click on Next button, and on the next window, enter the OTP code displayed on your token device.
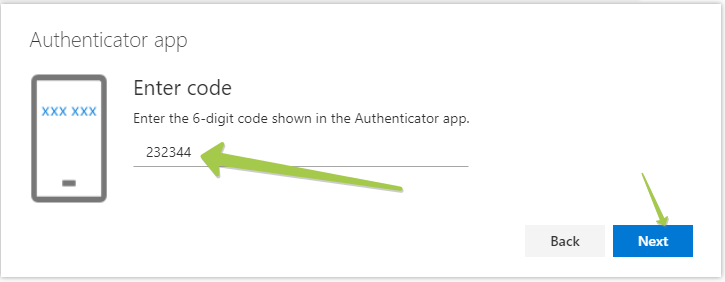
Complete the process by clicking on "Next" button.
Frequently asked questions
- Q. Do I need tenant admin rights in order to use hardware tokens with cloud-hosted Azure MFA?
- A. Not for cloud Azure MFA. Token2 programmable tokens fully emulate mobile apps, so it can be enabled (and disabled) by end users themselves.
- Q. Can the programmable token be reused for another user (i.e. if the previous owner left the company)?
- A. Yes. the programmable tokens are reprogrammable for an unlimited number of times. So the steps described above can be repeated for any user using any Token2 programmable device (even previously owned).
- Q. Why does the burner app crash when I scan the QR code?
- A. The QR code shown by default on this page is in Microsoft's proprietary format (phonefactor protocol) and is not compatible with the QR reader component of our app. Please make sure you switch to "Configure app without notifications" mode before scanning the QR code.
- Q. Can I use both hardware and software token simultaneously?
- A. Yes, as long as "Configure app without notifications" option is maintained. When you see the QR code after clicking "Configure app without notifications" you can scan it using a mobile app (such as Google Authenticator or Token2 Mobile OTP) before continuing with burning the seed on the programmable token.
- Q. Can other types of hardware tokens (for example c202) be used with Azure MFA?
- A. Onprem hosted MFA server (Azure MFA Server) supports any TOTP tokens, however, cloud Azure MFA is currently in public preview. Refer to this blog post for more details. Worth mentioning that the same tokens can be easily reused even after this feature becomes available.
- Q. Is there support for time drift and time skew of the hardware tokens in Office 365 with Azure MFA?
- A. We have tested the accepted skew with Azure MFA using our TOTP Toolset and discovered that the allowed skew around 900 seconds (15 x 30-second steps in each direction) which means that no adjustment is needed. If you still need the time to be accurate, you can use our programmable hardware tokens with time sync feature
- Q. Why a hardware token more secure than other methods such as mobile apps, texts or voice calls?
- A. Physical hardware tokens are a much more secure protection a user can currently have. A separate, isolated device generates OTP codes fully offline without any need for Internet or any other network access. There is no potential way for attacker access nor infect the device or intercept the generated one-time passwords. In case a hardware token is lost or stolen the user will notice it right away. This is not the case with a mobile app running on an infected mobile device or a text message intercepted at the GSM network level; with these methods, the victim may not even be aware of the attack at all.
azure mfa hardware tokens
office 365 mfa hardware tokens,
office365 mfa hardware token,
hardware tokens for azure mfa,
hardware tokens for office 365
Subscribe to our mailing list
Want to keep up-to-date with the latest Token2 news, projects and events? Join our mailing list!

